Diwali Special Offer – Flat 20% OFF on VPS Hosting + Free .in & .co.in Domain
Get Quote
DDoS Protection For Servers and Remote Networks
DDoS Protection for servers has become a required service for many online industries, including gaming (Minecraft, Counter Strike, Spigot etc), healthcare and e-commerce websites. With Everdata True DDoS Protection, we are able to mitigate layer 3/4 attacks as well as the effectively protect against the hard to detect layer 7 that attack applications using only a small amount of bandwidth.
Remote DDoS Protection is also available for clients who require mitigation services at their own facility. Using GRE tunnels, we can divert traffic to our network for inspection, analysis and filtering to ensure high availability of your online business or project. Click on the Remote DDoS Protectiontab to get started or get a quote to learn more about about our DDoS mitigation services.

Remote DDoS Protection For Networks
- Remote DDoS protection based on GRE tunnel
- Quickly get started with simple LOA (Letter of Authorization)
- DDoS protection of up to 500 Gbps attack
- Options include 10 Gbps, 20 Gbps, 30 Gbps, 40 Gbps, 50 Gbps, 100 Gbps and 500 Gbps
- Use advanced filtering tools to completely block protocols like UDP with anti DDoS firewall.
- True Layer 3, 4 and 7 protection
- Advance monitoring with DDoS reporting panel
- Block DDoS attacks such as HTTP floods, DNS flood, DNS amplification, NTP amplification, SSDP amplification, IP fragmentation, SYN flood, UDP flood, TCP, application layer etc
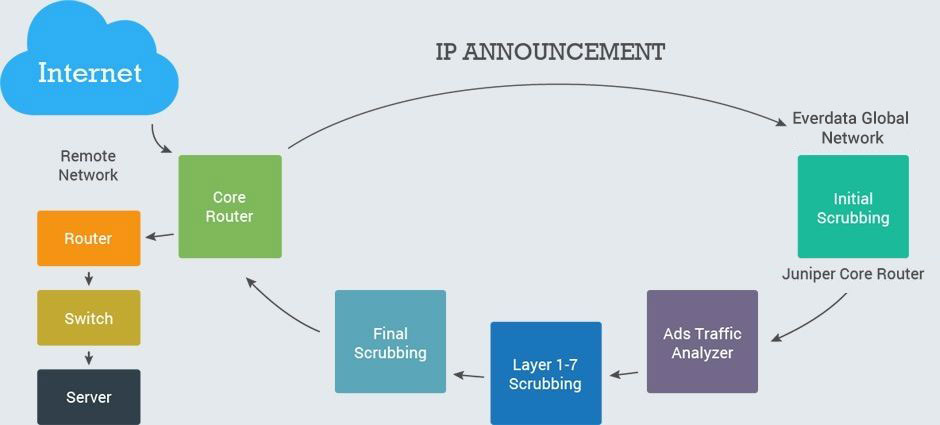
When it comes to protecting our customers, we’re not limited to just our facilities. We can employ the use of GRE Tunnels / Reverse Proxies. Using GRE Tunnels, we can remotely protect clients in facilities across the globe by re-routing malicious attack traffic to our scrubbing centers where we only send off clean traffic to its destination.
How Our Network Will Protects You?
Having scrubbing POPs placed throughout the globe allows our system to mitigate much larger attacks when necessary. Although we have the capacity of 200gbps in specific POP our peering level may have limited peering arrangements which may cause packet lost, re-transmissions, and latency issues when their peering arrangements are beyond their capacity. Therefore, with anycast DDOS systems we are able to direct traffic to multiple locations allowing our systems to utilize the "divide and conquer" method. This has worked during modern warfare, economics, and its one of the strategy
More options of scrubbing POPs will allow our GRE tunnels to reach your data center with less latency. An example is if your Data center or POP is in Texas you will pick our POP closest to you to reduce any unwanted latency. We provide a very robust capacity of network peering.
This allow us to deliver a protected network. Using our services from IP transit, Colocations, Dedicated server our customers has an ease of mind that we are able to defend against any attack. Anycast DDOS & Services has allow our customers to utilize its service to deliver content closest to the POP as well as mitigate attacks away from its origin.
DDOS MITIGATION FEATURES
-
 DDoS Mitigation
DDoS MitigationProtection against all known attacks, with a guaranteed minimum of 10 Gbps and 6,000,000 packets per second Heuristic based DDoS mitigation, enabling complete defense against all known and “zero day” threats 99.9% Best Effort SLA Standard 24/7/365 ticket or telephone support.
-
 Critical DDoS Mitigation
Critical DDoS MitigationPMulti-10G as needed to rapidly scale with dynamic customer requirements, enabling complete protection against any and all DDoS attacks.
-
 Attacks
AttacksHeuristic based DDoS mitigation, enabling complete defense against all known and “zero day” threats 99.99% Proactive SLA, guaranteeing the highest level of availability assurance, within the subscribed specification VIP Priority Support; receive immediate Tier 2/3 escalation on every call or ticket Direct to NOC “Batline” for critical requests Dedicated account executive
-
 Key benefits of network
Key benefits of networkPure ethernet architecture on a multi-10G backbone, leveraging only high performance Juniper MX routers Performance under fire: Network delivers 99.99% SLA despite high threat environment Dual stack IPv4/IPv6 enabled Static Layer 3 policies (ACL’s) allowing customers to define basic filters that are exported upstream edge networks Zero cost ingress transit, preventing overages resulting from DDoS attack traffic Low latency, high performance routes worldwide, with emphasis on Asia and mainland China Real time traffic and DDoS attack intelligence via the Attack Monitoring Platform
Anycast
DDOS PROTECTION
All packages with 100 Gbps or higher protection are automatically enrolled in global anycast DDoS protection. Our anycast feature will ensure that IP's assigned to your device is globally announced across Los Angeles, Dallas, Ashburn, London and Amsterdamn. This allows us to stop the attack before it even reaches the server.
Frequently Asked Questions
DDOS for Remote Networks
-
1
How does remote DDoS work?
Remote DDoS is for client's with a remote data center or host where they own the IP space. Instead of relocating the IP space, they can announce their IP into our network where we will scrub the dirty traffic and deliver the clean traffic over GRE tunnel back to your server or network.
-
2
What is required to get setup with remote DDoS protection?
You will need your own IP space, ASN, and a router that is able to do BGP (Border Gateway Protocol) and GRE (Generic Routing Encapsulation) tunnels. To get setup, we'll need an LOA (Letter of Authorization) authorizing the announcement of your IP block (prefix) on our network. Prefix is an IP block assigned to you from ARIN. LOA are Letter of Authorization where you will specify the prefix we are allowed to announce. The LOA must include your company letter head, ASN number, and a statement that says AS40676 is allowed to announce your prefix.
-
3
Is remote DDoS only for a network or can client's also protect a single remote server?
Your welcome to announce small prefixes such as a /24 which can be for one specific server or simply high risk clients who are under attack.
-
4
Is there a minimum requirement for a client to use remote DDoS protection?
Yes a minimum prefix of /24 along with a router that allows BGP and GRE is required to get started.
-
5
Is there is a cost associated with announcing and with drawing prefixes for remote DDoS?
When a tunnel along with GRE is built, you do not need to announce prefixes all the time. You can wait until an attack occurs where you can announce the prefix to initiate the mitigation process. note you can only announce a /24 which is the smallest a BGP route allows for a provider to recognize that prefix. There are no charges when announcing and withdrawing prefixes. The flexility is in the network operator's decision.

Get Risk Free Web Hosting With Our 7 Days Money-Back Guarantee
EverData, a top Web hosting and data center services company in India, provides a 7-day money-back guarantee on all our services. Our devotion towards client satisfaction is completely proven by our 7 days' money-back policy, which allows our clients to try out their services risk-free and make an informed decision about their web hosting needs.
